The Dangers of Copy/Paste Coding
One of my blogging hero’s Jeff Atwood blogged about this a few months ago, but it never really hit home for me until recently. I’m a “Don’t reinvent the wheel” kind of guy, I much rather spend time  building direct business value then working on plumbing. So being the blatant rip off artist that I am I use Google for answers to things I think are common.
building direct business value then working on plumbing. So being the blatant rip off artist that I am I use Google for answers to things I think are common.
I stumbled upon BouncyCastle a little while ago when trying to find a way to move away from Chilkat’s encryption library to one that would allow me to compile my assembly with the “Any CPU” flag. But to my dismay they have a very limited amount, bordering on none, of the samples and documentation I needed to use their library. So I turned to my old friend Google for some answers.
What Google returned for me was a post by Havard Stranden on his blog, someone who I’ve read before and even used his Copyable software before. Havard had exactly what I was looking for, and some code examples, I was so happy. So I begun the art of copy and paste and was on my way.
I’ve started to use Unit Tests a little more then in the past. I’m not part of the religion by any means, more of an observer waiting and watching for the spiked punch to be rolled out and the show to begin. I usually use Unit Tests to fix problems or reaffirm my knowledge, because I still didn’t have a lot of information on BouncyCastle I wrapped Unit Tests around my RSA encryption and started testing.
Well some of my Unit Tests failed and some others threw exceptions. I blamed everything but the code I copied and pasted from the Internet. I changed my encoding at least 5 times, I changed my wrapping and conversion functions another 5 or so times, and so on. I wasted about a week trying to figure out what was wrong, why could I correctly encryption and decrypt a small block of test, but not a larger one.
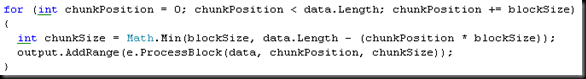
Finally I stepped into the code, line by line and observed what was occurring, and I finally found the issue. This was the inner loop of my encryption and decryption methods, which basically chunk through and array and encrypt and decrypt each chunk. Can you guess where the problem was?
What I found out was chunkSize was going negative, or to zero, a lot. If what I was encryption was less then the blockSize, which is how many parts of the array the RSA encryption function can handle at a time, the I was good. But if it was a larger amount of data it would completely bomb out.
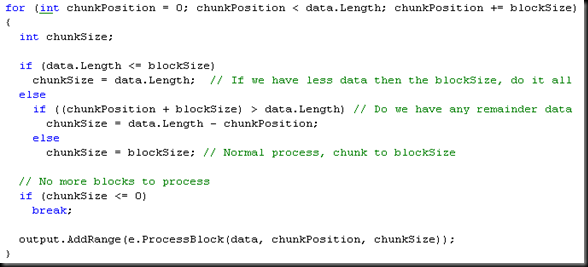
What I ended up with was more then I think one line can handle, but I could be wrong. Basically there were three cases I saw, and I put some if statements in to handle them.
I don’t know why I didn’t dawn on me to check my copy/paste programming first, but I’m so used to finding code that just works I rarely check to to ensure it does. The code probably was a quick sampling or a mock up and not his actually production code. I have no idea where it came from but assuming it was ‘live’ code was the wrong thing to do. When I started having problems that’s probably the first thing I should have looked at, as it was the only thing I didn’t completely understand or write myself.
So word to the wise all you Copy/Paste programmers, check from time to time to ensure the code works properly, else you could burn many hours tracking down issues.
P.S. Sorry Havard, but I don’t know the Alt code for that special A.
Hi Shawn, seems you’ve hit a bug in the sample code. I’ll try and find time to fix it, really busy these days (as you can probably tell from the date of the last blog post at my site).
Assuming that code found online is bug free and production ready is very dangerous, and you should always at least write unit tests that cover your use cases for the code. For one thing, people make mistakes. Also, most blog posts with code examples obviously don’t contain production quality code, but are rather made up there and then.
Oh, and no worries about the misspelling of my name. 🙂 The a with the ring on top is the Norwegian character å, Unicode U+00E5 (or Alt+0229, if you prefer that.)